In the ever-evolving world of web security threats, **CSS exploit** has emerged as a concerning topic for developers and users alike, especially in light of the recent CVE-2026-2441 vulnerability reported in Google Chrome. This particular CSS vulnerability exploits weaknesses within the browser’s rendering engine, allowing malicious actors to potentially execute harmful scripts under certain conditions. As web security becomes increasingly paramount, understanding this CSS exploit is crucial, given that it underscores the fragility of seemingly harmless web technologies. With Chrome’s robust security measures constantly being tested, this incident highlights the ongoing battle against browser exploits and emphasizes the need for user vigilance. Addressing such vulnerabilities is not merely an option but a necessity to safeguard sensitive data and maintain safe browsing experiences for all.
When discussing vulnerabilities within web technologies, the term **CSS exploit** may seem alarming, yet it points to a broader issue of browser security. Many users may think of these issues as merely abstract concerns, but incidents like the recent **CSS vulnerability** in Chrome bring them to the forefront of web security discussions. In this context, the focus shifts to the underlying mechanisms that could allow a **browser exploit** to take place, emphasizing the importance of keeping browsers updated. With the rapid pace at which web security threats evolve, understanding these complex interactions within the **Chrome security** framework is essential for developers and everyday users to protect themselves from cyber dangers. Vigilance against these vulnerabilities is a collective responsibility, highlighting the critical nature of web application security.

Understanding the CSS Vulnerability
In the realm of web development, CSS has generally been regarded as a benign and essential tool for enhancing the presentation of web pages. However, the recent reports highlighting a CSS-based exploit in Chrome have sent ripples through the community. This vulnerability, designated CVE-2026-2441, has created an uproar due to its potential implications. Interestingly, the idea that CSS can be exploited in such a manner raises eyebrows among developers who rely on its established safety. After ensuring the browser updates, the question that looms large is: how did a simple stylesheet become a possible vector for attack?
To grasp the intricacies of this issue, it’s vital to dissect the essence of the vulnerability. Reports seem to suggest that CSS was at the root of the problem, leading many to infer that malicious styling could execute harmful commands. However, the truth is slightly more nuanced. It wasn’t CSS itself that posed the threat; rather, it was the way the browser’s rendering engine mishandled certain CSS constructs that led to a memory safety bug. This distinction is critical, as it underscores the importance of understanding the interplay between CSS and JavaScript, where the latter retains the power to execute potentially harmful operations.
Debunking the Clickbait Myths
As the news of this exploit circulated, various headlines sensationalized the incident, framing it as a straightforward CSS exploit. This framing drawn from the sensationalist playbook may have caused unnecessary alarm among web developers and website owners. The temptation to paint it as a pure CSS issue plays into our fears of web vulnerabilities, which can exploit any code we write. Yet, upon deeper examination, it’s clear that the CSS aspect contributed only indirectly to the risk, primarily facilitating a context where JavaScript could perform its dubious deeds.
Moreover, the misconception stems from incomplete explanations that ignore the underlying mechanics of how CSS interacts with browser processes. For example, the report showcased a fictional, malicious CSS rule that simply isn’t feasible under standard browser protections. Readers may find themselves anxiously pondering the idea of styling rules as active threats instead of viewing CSS through its original lens: a method for structuring and styling content without causing harm.
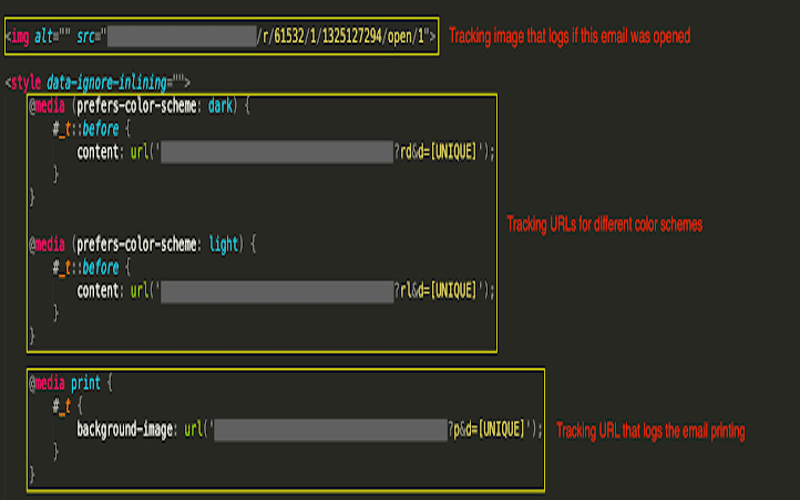
How the Exploit Functioned
The crux of the exploit resides not only in the CSS but primarily in the underlying JavaScript functionality that parses and executes CSS rules. Within the Chrome’s Blink rendering engine, a specific sequence in handling `@font-feature-values` led to a flaw. With this vulnerability, an attacker could exploit the condition to run malicious scripts, circumventing the originally intended protections of memory segmentation. Ultimately, this led to scenarios where scripts could gain unauthorized access to resources that they should never see, exacerbating the gravity of the situation.
Parsing CSS, while ostensibly straightforward, can yield unforeseen consequences when an error in memory management occurs. Chrome’s handling of CSS rules through JavaScript opens a window for vulnerabilities that can ultimately lead to crashes or denials of service if exploited. As discussed, understanding the mechanics behind this exploit is not merely an exercise in technicality but a necessary step in reinforcing vigilant coding practices to preemptively combat such exploitation.
The Patch and Future Safety
In response to the vulnerability, the team behind Chrome promptly issued a patch to mitigate the risk posed by this exploit. This quick turnaround was vital as it addressed the underlying flaws in the memory management of the rendering engine. The one-liner fix aimed to substitute the problematic `HashMap` data structure with a safer alternative, effectively fortifying the browser against not just this incident but also similar potential threats inherently linked to UAF (Use After Free) vulnerabilities.
However, the discovery of this exploit does raise critical questions about the state of web security moving forward. It serves as a reminder that even widely trusted technologies like CSS can harbor unexpected risks. As developers, we must continuously evaluate and update our security measures to address the evolving landscape of web vulnerabilities. The industry should look for a more holistic approach to security that prioritizes not only patching but preemptive design principles that safeguard against both known and undiscovered risks lurking in the shadows.
Conclusion: Staying Vigilant
As we reflect on the implications of the recent CSS exploit, it’s essential to recognize the dual nature of technology. While CSS remains an invaluable tool for web design, this incident starkly illustrates that even the most trusted elements can harbor hidden dangers. The interplay between CSS and JavaScript requires diligent engineering and constant vigilance to ensure our websites don’t become unwitting conduits for malicious activities.
Moving forward, it’s imperative for all web developers to stay informed about vulnerabilities, engage in routine updates, and prioritize security in the design phase. The world of web development is ever-evolving, and with that evolution comes new challenges. Let us embrace a culture of continuous learning and adaptation to navigate the web safely and effectively.
In conclusion, while the recent CSS exploit reported in Chrome has raised concerns about the security of web technologies, it is crucial to understand the nuances involved in this case. Although CSS played a role in triggering a vulnerability, the exploit itself hinges mainly on underlying JavaScript and memory management issues within Chrome. To summarize important points from this discussion:
– **Role of CSS**: The exploit indicated was not a direct CSS attack; rather, CSS parameters interacted with JavaScript vulnerabilities.
– **Memory Management Flaws**: The exploit originated from a bug in Chrome’s memory handling related to the `CSSFontFeaturesValueMap`, demonstrating how complex interactions between languages can lead to security risks.
– **Patch Implementation**: Chrome has since issued a patch that aims to rectify the vulnerability, shifting to a safer code structure to enhance security and manage memory better.
As technologies continue to evolve, our approach to security must likewise adapt to ensure users remain protected from potential exploits.
Thus, while the situation surrounding this CSS-related exploit might seem alarming at first, it highlights broader themes in web security that demand our attention. Understanding these complexities helps prevent misconceptions and fosters a more informed discourse on web security. Key takeaways include:
– **Discrepancy in Reporting**: Many headlines oversimplified the nature of the exploit, leading to confusion between CSS and JavaScript roles.
– **Need for Vigilance**: Users are urged to keep their browsers updated to safeguard against newly discovered vulnerabilities, as exploits can surface unexpectedly.
– **Future Concerns**: Given the recurring nature of UAF (Use After Free) problems in Chromium, continuous efforts in code refinement and comprehensive security audits are necessary as we advance.
In essence, while we can breathe a little easier today, the evolving landscape of web vulnerabilities requires an ongoing commitment to security best practices.